AI-Powered Cybersecurity Tools Every Business Needs
It is crazy to think about how much things have changed in just the last few years. Back in the day, people used to think of cyber-attacks as just an IT issue that the tech guys in the basement would handle. But here we are in 2026, and that is definitely not the case anymore. Today, a cyber-attack is a major business risk that can shut down a whole company. The problem is that these attacks are happening at a scale we have never seen before. They are faster, they are more automated, and they are way harder to catch if you are still using the old-school rule-based security systems that we used to rely on.
Traditional security tools usually work by following a specific set of instructions, like blocking a certain IP address or looking for a specific pattern in malware. While that stuff is still important, it just does not cut it anymore. Hackers have figured out how to get around those rules by using legitimate login credentials or running very slow and quiet attacks that take weeks to finish. These rule-based systems also tend to create so many alerts that the actual human security teams get totally overwhelmed. AI-based cybersecurity solutions are the answer to these gaps because they do not just follow a list of rules. Instead, they learn and detect threats that would have totally gone unnoticed in the past.
The big shift here is that AI focuses on behavior instead of just looking for a list of known threats. To give you an idea of how this works, think about a normal day at the office. If an employee logs on at 9 a.m. from New York, the system knows that is normal behavior for them. But if that same account suddenly logs on at 2 a.m. from somewhere in Eastern Europe and starts downloading thousands of files, the AI is going to notice that immediately. It sees the anomaly in real time, even if it is a brand-new type of attack that no one has ever seen before. This article is going to walk you through the AI-based tools that every modern business should be looking at right now and explain how they actually help you stay safe without costing a fortune.
The Big Benefits of Using AI in Your Security
Before we dive into the specific tools, we should talk about why everyone is so obsessed with AI in the first place. A lot of people are talking about big data, but the real benefits are much more practical. One of the biggest wins is faster detection. These systems can see an event and react to it almost instantly, which is way faster than a human could ever do. Another huge plus is that you get fewer false positives. Because the AI learns what normal looks like for your specific business, it stops crying wolf every time something tiny happens.
Automation is another game-changer. There are systems out there now that can automatically isolate a compromised device or lock down an account the second they see something suspicious. This means a breach can be stopped before it even spreads. Plus, AI is incredibly scalable. You do not need to hire a hundred new people to watch every single event because the software can handle millions of events on its own. For small and medium-sized businesses, this is a huge equalizer. It gives smaller teams the same kind of protection that the giant tech companies have, helping them stand up against attackers who might have more resources.
1. AI-Enhanced Endpoint Detection and Response
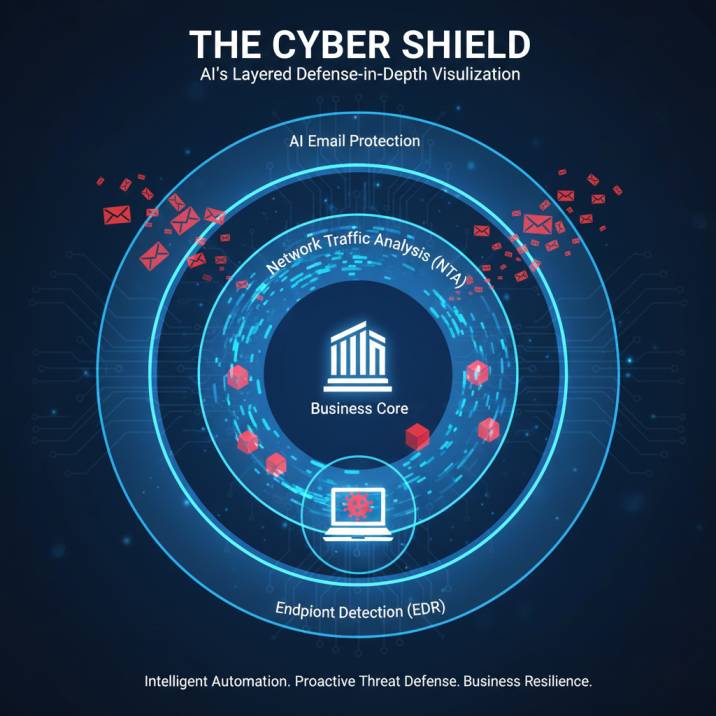
The first tool you really need to know about is AI-Enhanced Endpoint Detection and Response, or EDR for short. Basically, these tools are built to watch over all the computers, laptops, and servers in your network. But they do not just look for viruses. They are actually monitoring things like how processes behave, how much memory is being used, and what kind of internet connections are being made. They even keep an eye on what users are doing over time to make sure nothing looks off.
Let's look at a real-world example to see how this works. Imagine someone on your finance team opens a PDF that looks totally normal. A traditional antivirus might look at that file and think it is fine because it doesn't match any known malware signatures. But once that PDF is open, it might try to use PowerShell to talk to a weird server somewhere else. An AI-driven EDR will see that behavior as suspicious right away. It identifies the activity, realizes it is not what a finance person should be doing, and then automatically quarantines the device before any damage is done.
If you are going to use EDR, you should make sure to deploy it on every single endpoint, not just the laptops your employees use. It is also a good idea to enable the automatic isolation feature for any threats that the system is really sure about. You do want to check the list of blocked behaviors every now and then, just to make sure the AI isn't accidentally stopping a legitimate business app from working, but generally, it makes things much smoother. Common examples you might have heard of include CrowdStrike or Microsoft Defender for Endpoint.
2. Network Traffic Analysis Based on AI
Next up is Network Traffic Analysis, or NTA. Think of this as a tool that monitors the flow of information across your entire network. It looks for inconsistencies and alerts you when something feels wrong. This could be unusual data being moved around, or someone trying to move laterally through your systems to get from a low-security area to a high-security one. It basically identifies what the normal traffic pattern looks like and then flags anything that doesn't fit that mold.
Here is a scenario: a malicious user manages to break into a server that doesn't have many privileges. They are smart, so they don't launch a virus. Instead, they just spend weeks quietly scanning the network to see what they can find. Since there is no malware, a traditional system won't send any alerts. But an AI-driven NTA tool will notice that this server is suddenly making a lot of internal links that it never made before. It catches the unusual activity before the hacker can get into your most critical systems.
When you start using NTA, it is best to begin in a monitoring mode so the system can establish what a clean mark looks like for your network. You should also make sure you are focusing more on the internal traffic anomalies rather than just looking at what is coming in from the internet. Integrating this with your other security systems, like a SIEM, will make it even more effective at spotting the bad guys.
3. AI-Based Identity and Access Management
Identity and Access Management, or IAM, is all about making sure that the people logging into your systems are actually who they say they are. AI versions of these tools look at login actions to find things that don't make sense. For instance, they can detect what is called impossible travel. This is when someone logs in from New York and then tries to log in from London ten minutes later. Unless they have a teleportation device, that is a huge red flag. They also look for unusual login times or people trying to give themselves more permissions than they should have.
Imagine an employee has a weak password that gets stolen. To the system, the login looks legitimate because the password is correct. However, the AI engine will notice that the login is happening at an odd time or from a device that the employee has never used before. Instead of just letting them in, the AI will trigger a step-up authentication, like asking for a secondary code, or it might just reject the login entirely.
To get the most out of this, you should enable risk-based authentication instead of just using static rules for multi-factor authentication. It is also really important to have strict guidelines on how AI is used for your most sensitive accounts, like those in admin or finance. By regularly analyzing the access logs for patterns that the AI has discovered, you can stay one step ahead of anyone trying to hijack an account. Popular options here include Okta Adaptive MFA, Azure AD Identity Protection, and Ping Identity.
4. AI-Driven Email Protection
Even in 2026, email is still the number one way that hackers try to get into a business. AI-driven email protection is a must because it doesn't just look for bad links. It actually analyzes the writing style and the intention of the email. It looks at how the sender has behaved over time and can even spot refined phishing attacks that are designed to bypass keyword filters by using clever language.
You might get an email that looks like an invoice from a seller you actually use. It might even imitate their exact writing style. A conventional filter would probably let it through because it looks so real. But the AI will see that something is slightly off with the pattern and alert the user before they have a chance to click on anything dangerous. This kind of proactive defense is so much better than just reacting after a mistake is made.
To make this work well, you should let the algorithm learn from your company's historical email data. You should also enable scanning after delivery, just in case a threat is detected a little bit later. And of course, you should always combine this technology with phishing awareness courses for your team. Using tools like Microsoft Defender for Office 365 or Barracuda Email Protection can really help lower the risk of someone accidentally letting a hacker in through their inbox.
5. AI-Powered Security Information and Event Management
Security Information and Event Management systems, or SIEM, are basically the brains of the operation. They record logs from everywhere in your environment. AI makes these systems way more useful because it can link different incidents together across multiple systems. It scores risks based on patterns and helps the security team focus on the most important incidents instead of getting lost in a sea of data.
Think about a situation where you have a few failed login attempts, a firewall alert, and a request to access some sensitive data. On their own, each of these things might look harmless. But when you put them all together, the AI sees them as one continuous attempt to breach your system. It connects the dots that a human might miss and flags the whole situation as a major threat.
To avoid getting overwhelmed by alerts, you should tune the AI scoring thresholds to fit your specific needs. It is best to focus on specific use cases like ransomware or insider threats. You should also try to automate as many of the simple responses as possible. This lets your team spend their time on the big problems while the AI handles the routine stuff. Common tools in this category include Splunk with its ML Toolkit, IBM QRadar, and Sumo Logic.
6. Fraud Detection with AI
Fraud detection used to be something that only banks really cared about, but now it is something that almost every business needs. AI-powered fraud detection is great at spotting things like fraudulent user accounts, abnormal transactions, or people who are trying to abuse your promotions and services. It creates a behavioral fingerprint for users, which makes it much harder for scammers to hide.
For example, an e-commerce site might notice hundreds of test purchases being made. Even if they are using different accounts, the AI can see that they all share the same behavioral fingerprint. This allows the system to halt the attack before any actual fraud occurs. It is a very powerful way to protect your revenue and your reputation.
When you are setting this up, it is important to develop acceptable risk levels rather than trying to exclude everything, because you don't want to block real customers. You should keep a close eye on false positives to make sure you are protecting your regulars. As customer behavior shifts over time, make sure you are enhancing your models so they stay accurate.
How to Choose the Right Tools for Your Business
You don't need to go out and buy every single tool on this list the second you start up. It is much better to start with your actual risks rather than just following the hype. You should ask yourself what information would be the most damaging if it got leaked and where your biggest entry points are. You also want to look at which alerts are currently bogging down your team so you can find tools that actually help them save time.
Integration is also super important. AI tools work best when they can talk to each other. When you are looking at suppliers, check for things like open APIs and native integration with the systems you already use. Budget is another big factor. While AI will definitely save you money in the long run by preventing attacks, the initial costs can be different depending on the provider. A good tip is to look for suppliers who offer tiered pricing or even free trials so you can test the tools out before you commit to a big purchase.
In the end, AI-powered cybersecurity is no longer a luxury. It is a necessity for any business that wants to survive in 2026. Since attacks are getting faster and more sophisticated every day, you just can't rely on systems that don't have the ability to think and learn. A smart strategy isn't about buying every AI tool on the market, but about finding the ones that fit your risk profile and using them alongside your human team. When you do it right, AI doesn't replace your security people. It just makes them better and helps everyone feel a lot more secure.